Have you heard of Stuxnet? Unless you run industrial or power control systems, the emergence of this nasty little piece of malware probably didn’t even cause the slightest blip on your radar. But that’s no reason to ignore it.
Stuxnet targets Siemens Simatic WinCC, a Windows-based suite of software that’s used by industrial plants and power utilities. It piggy-backs on the Windows .lnk vulnerability that made huge headlines this summer and caused Microsoft to scramble for a fix. The fact that it can grant an attacker remote access is worrisome enough, but it can also alter the Programmable Logic Controllers (PLCs) in automation hardware attached to those PCs. And that can spell real trouble.
Cnet’s Elinor Mills spoke to Liam O’Murchu, manager of operations for Symantec Security Response and he paints is a chilling picture.
“For example, at an energy production plant, the attacker would be able to download the plans for how the physical machinery in the plant is operated and analyze them to see how they want to change how the plant operates, and then they could inject their own code into the machinery to change how it works,” he said.
His team is still analyzing the code, but so far he reports that Stuxnet appears to be capable of date-based actions. Creepy! More troubling is the fact that there are companies that have already been infected, casting a shadow over their own cybersecurity policies.
Moreso, this is also a lesson for smart grid tech firms. Not only will they want to be mindful of their own code, but they may also want to carefully consider the underlying software that they employ. It’s not inconceivable for a home management gateway startup to develop an Android-based dashboard, hypothetically speaking. Why worry? Because, as recent discoveries of some serious vulnerabilities in Android and Apple’s iOS show — both popular mobile OSes for the EV charging/connected car and energy management crowd — no software is immune to a determined hacker. Just something to consider.
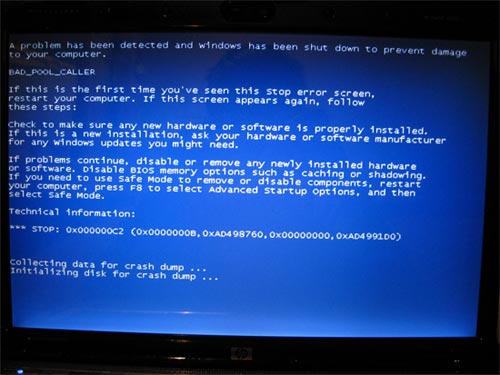
Image Credit: coolmikeol – Flickr – CC

[…] you’ve been following IT security lately, you’ve undoubtedly heard of Stuxnet. The worm is currently sparking some cybersecurity drama with a sprinkling of geopolitical […]